Only 16% of respondents in the UAE and Saudi Arabia say they are able to keep pace with the threat landscape, far behind the global average (40%)
Delinea, a leading provider of Privileged Access Management (PAM) solutions for seamless security, today announced findings from a global survey of 2,100 IT Security Decision Makers (ITSDMs) which reveals that 60% of respondents believe their overall security strategy does not keep pace with the threat landscape, and that they are either lagging behind (20%), treading water (13%), or merely running to keep up (27%). Conducted in more than 20 countries, the research polled attitudes towards identity security and the protection of privileged identities.
The report also highlights differences between the perceived and actual effectiveness of security strategies. While 40% of respondents believe they have the right strategy in place, 84% of organisations reported that they have experienced an identity-related breach or an attack using stolen credentials during the previous year and a half.
Compared to other countries, respondents from the UAE and KSA show a higher level of scepticism toward their security strategies, as more than half (53%) believe their overall security strategy is ‘in the doldrums’ and requires a re-invigoration of cyber security across the organisation, with only 16% stating they are able to keep pace with the threat landscape. At the same time, a staggering 91% reported that they experienced an identity-related breach or an attack using stolen credentials during the previous year and a half.
Identity security is a priority, yet board buy-in is critical
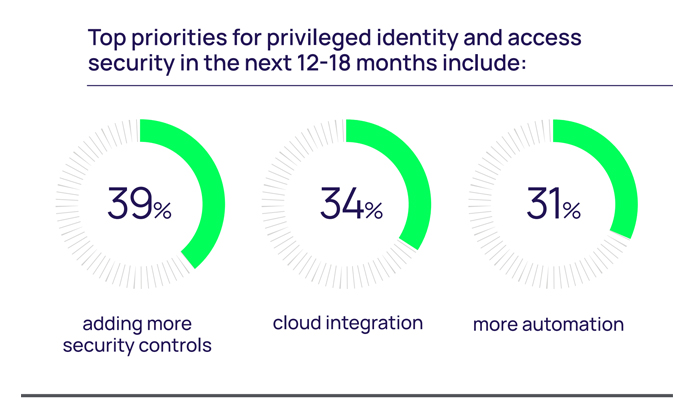
Promisingly, many organisations are hungry to make a change, particularly when it comes to protecting identities. In line with the global findings, 94% of UAE and Saudi respondents (90% globally) state that their organisations fully recognise the importance of identity security in enabling them to achieve their business goals, and 86% say that it is one of the most important security priorities for the next 12 months.
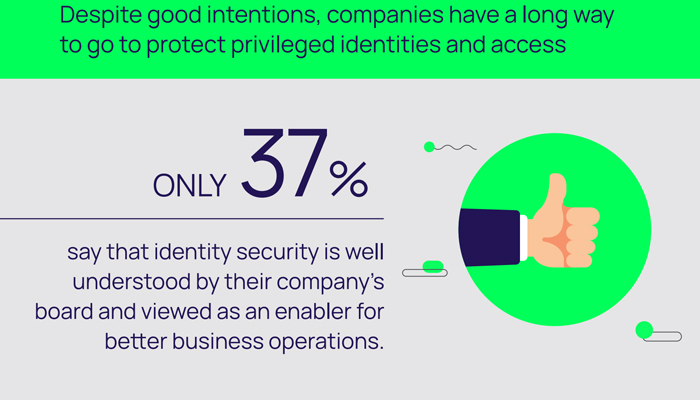
However, 85% of UAE and Saudi respondents (75% globally) also believe that they’ll fall short of protecting privileged identities because they won’t get the support they need. This is largely due to a lack of budget and executive alignment, with 68% of regional respondents saying that their company’s board still doesn’t fully understand identity security and the role it plays in enabling better business operations.
“While the importance of identity security is acknowledged by business leaders, most Middle East security teams will not receive the backing and budget they need to put vital security controls and solutions in place to reduce major risks,” comments Joseph Carson, Chief Security Scientist and Advisory CISO at Delinea. “This means that the majority of organisations will continue to fall short of protecting privileges, leaving them vulnerable to cybercriminals looking to discover privileged accounts and abuse them.”
Lack of policies puts machine identities at great risk
The research reveals that, despite good intentions, companies have a long way to go to protect privileged identities and access. Less than a third (31%) of the regional organisations surveyed have implemented ongoing security policies and processes for privileged access management, such as password rotation or approvals, time-based or context-based security, or privileged behaviour monitoring such as recording and auditing. Even more worryingly, exactly half of all UAE and Saudi organisations surveyed allow privileged users to access sensitive systems and data without requiring multi-factor authentication (MFA).
The report brings to light another dangerous oversight. Privileged identities include humans, such as domain and local administrators, as well as non-humans, such as service accounts, application accounts, code, and other types of machine identities that connect and share privileged information automatically. However, only 52% of UAE and KSA organisations manage and secure machine identities, while a concerning proportion leave them exposed and vulnerable to attack.
Carson added, “Cyber criminals look for the weakest link and overlooking ‘non-human’ identities—particularly when these are growing at a faster pace than human users—greatly increases the risk of privilege-based identity attacks. When attackers target machine and application identities they can easily hide, moving around the network to determine the best place to strike and cause the most damage. Organisations need to ensure machine identities are included in their security strategies and follow best practices when it comes to protecting all their IT ‘superuser‘ accounts which, if compromised, could bring the entire business to a halt.”


