As geopolitical tensions rise across the Middle East, Check Point Research (CPR) has identified a surge in cyber‑espionage activity by China‑nexus advanced persistent threat (APT) actors, with Qatar emerging as a primary target. The escalation coincides with the launch of Operation Epic Fury, with malicious campaigns beginning within 24 hours of the renewed conflict.
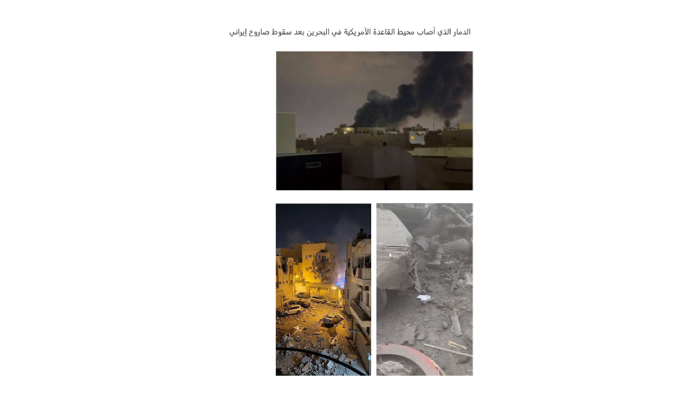
According to CPR, the China‑linked threat cluster Camaro Dragon rapidly deployed lures tied to missile strikes in Bahrain to target Qatari entities. Attackers distributed an archive disguised as photos of alleged Iranian missile strikes on U.S. bases, embedding a malicious LNK file that triggered a multi‑stage infection chain. The attack culminated in the deployment of PlugX, a long‑running modular backdoor widely associated with Mustang Panda, Earth Preta, and other China-nexus groups since 2008.
PlugX provides attackers with significant post‑compromise capabilities, including remote command execution, keystroke logging, file exfiltration, and screen capture. CPR notes that the sample used distinctive configuration keys previously linked to Camaro Dragon operations.
This Bahrain‑themed lure was not isolated. CPR identified earlier campaigns in December targeting Turkish military entities using the same infection vector, suggesting a broader Middle East focus that is now shifting toward Qatar as the region’s strategic landscape evolves.
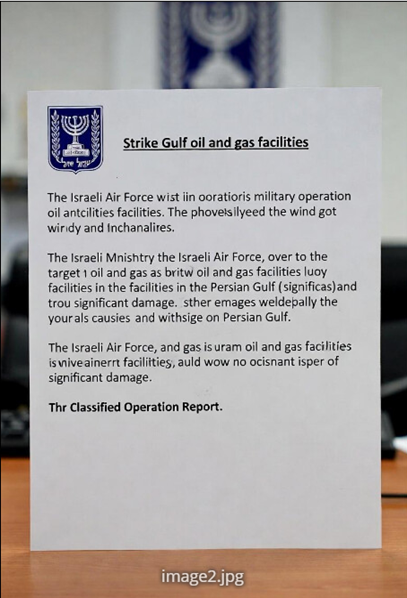
In a second campaign, attackers used a password‑protected archive titled Strike at Gulf oil and gas facilities.zip likely delivered via email to deploy a previously unseen Rust‑based loader impersonating documents from the Israeli government. The loader exploited DLL hijacking of nvdaHelperRemote.dll, a technique rarely observed but previously connected to China‑aligned groups delivering the Voldemort backdoor and conducting operations in the Philippines and Myanmar.
The final payload in this attack was Cobalt Strike, commonly used by both red teams and malicious actors for rapid reconnaissance and lateral movement.
Although CPR assesses the second campaign as China‑aligned with low confidence, overlapping tactics including NVDA DLL hijacking and infrastructure registered via Kaopu Cloud and Cloudflare support the attribution.
CPR concludes that China‑nexus espionage actors are rapidly pivoting toward Qatar, likely driven by intelligence collection priorities tied to the evolving regional crisis.