Infoblox Threat Intel researchers have uncovered a new phishing technique that bends one of the internet’s most fundamental systems into an attack vector. The campaigns exploit a part of the global domain name space never intended for hosting content, allowing cybercriminals to bypass many of today’s standard security checks with alarming ease.
The method centers on abuse of .arpa, a top-level domain reserved strictly for internet infrastructure. Unlike familiar domains such as .com or .net, .arpa is used for reverse DNS lookups, mapping IP addresses to domain names. It is not meant to host websites or user-facing content. Yet threat actors have identified weaknesses within certain DNS record-management systems that allow them to insert IP address records for .arpa domains—and then host malicious phishing sites behind them.
“When attackers start abusing .arpa, they’re weaponizing the very core of the internet and most defenses aren’t even looking there.”
— Dr. Renée Burton, VP, Infoblox Threat Intel
Attackers pair this maneuver with free IPv6 tunnels, services originally designed to help devices communicate across older IPv4 networks. By obtaining a large pool of IPv6 addresses, the actors rotate infrastructure rapidly and operate at a scale that traditional filters struggle to track.
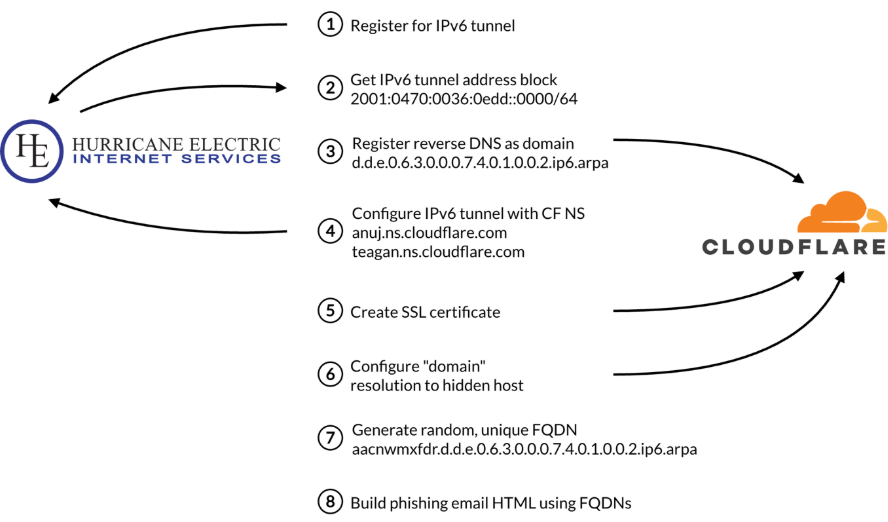
“The phishing emails look simple, but the infrastructure behind them is anything but,” Burton explained. The observed campaigns impersonate major brands, using a single embedded-image email that directs victims through traffic distribution systems before landing them on fraudulent websites. Because the visible link never exposes the underlying .arpa‑based strings, both users and security tools overlook the unusual domain usage.
Reverse DNS records are rarely inspected by reputation engines or URL classifiers, giving attackers a quiet path to operate. This makes the technique particularly dangerous: while organizations invest heavily in detecting malicious top-level domains or filtering suspicious URLs, few monitor the infrastructure layers that .arpa governs.
Infoblox warns that defenders must now treat DNS infrastructure itself not just the domains people see as a critical attack surface. As phishing tactics evolve beyond familiar patterns, security teams will need deeper visibility into unconventional DNS behavior to detect and disrupt these emerging threats.


