MEA sees over 80% of phishing activity targeting internet and financial services, fueling identity compromise and downstream supply‑chain breaches
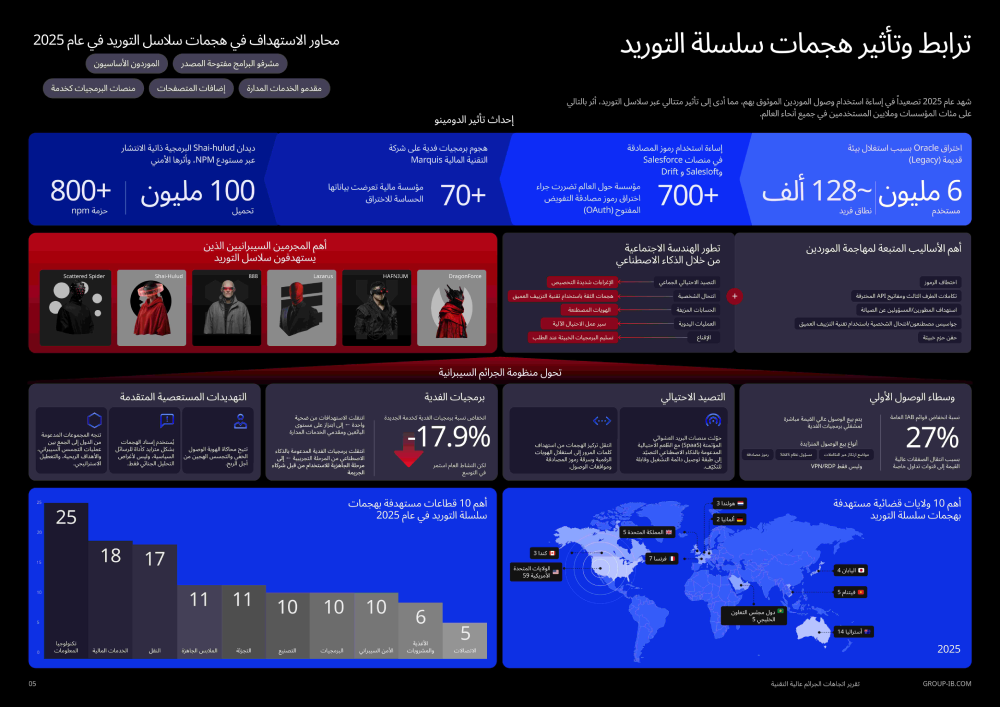
Group‑IB has released its High‑Tech Crime Trends Report 2026, revealing a profound shift in the global cyber threat landscape as supply chain attacks emerge as the most critical and disruptive form of cybercrime. The findings highlight escalating systemic risk for organizations across the Middle East & Africa (MEA), where accelerating cloud adoption and digital transformation are widening the attack surface across interconnected ecosystems.
The report outlines how attackers are exploiting trusted vendors, open‑source libraries, SaaS platforms, browser extensions, and managed service providers to infiltrate multiple downstream targets from a single compromise. Group‑IB’s telemetry from 2025 shows that phishing continues to be the primary gateway for these attacks, with threat actors disproportionately targeting internet services (52.49%), financial institutions (28.50%), and logistics organizations (11.20%). While the initial compromise often begins with an individual user, the downstream impact can quickly ripple across partners, customers, and third‑party networks.
“Cybercrime is no longer defined by single breaches it is defined by cascading failures of trust.”
— Dmitry Volkov, CEO, Group‑IB
In the MEA region, the threat environment is further complicated by the rise of Initial Access Brokers (IABs). More than 200 cases of corporate access linked to regional organizations were advertised for sale in 2025, enabling ransomware operators, espionage groups, and cybercriminal collectives to launch follow‑on attacks at scale.
Ransomware ecosystems also became more industrialized, with over 100 incidents reported in the GCC alone. The most targeted sectors included real estate, financial services, manufacturing, government, and healthcare. Meanwhile, supply chain attacks directly impacted at least five GCC organizations in IT and industrial sectors, with broader ecosystem consequences that remain difficult to fully quantify.
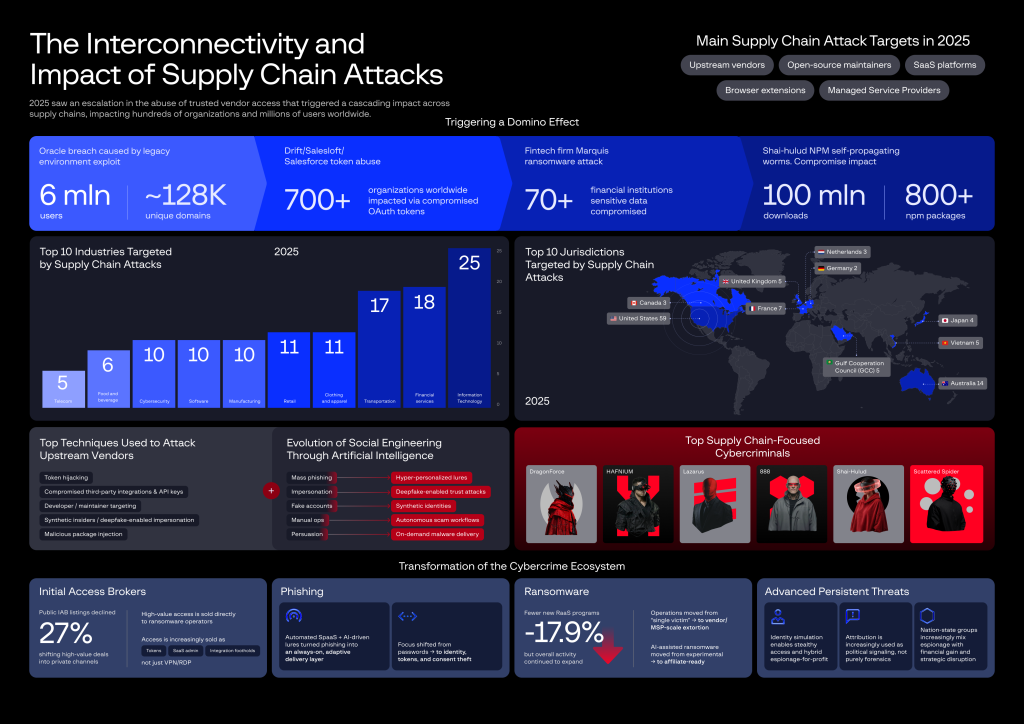
The report also highlights the weaponization of open‑source ecosystems, malicious browser extensions, OAuth token abuse, and AI‑driven phishing, alongside campaigns by groups such as Lazarus, Scattered Spider, HAFNIUM, DragonForce, and 888.
Group‑IB stresses the need for MEA organizations to prioritize identity security, third‑party risk governance, and continuous vendor monitoring, as supply chain compromise becomes the defining cyber threat of 2026.


